In today’s fast-paced advanced environment, businesses continually update their frameworks, taking off behind obsolete equipment that requires legitimate IT transfer. From ancient tablets and desktops to servers, capacity gadgets, and organizing hardware, falling flat to handle these resources accurately can uncover organizations to critical dangers, counting information breaches, administrative non-compliance, and natural hurt. Organized IT resource transfer methodologies offer assistance businesses efficiently oversee resigned IT Disposal, guaranteeing that each gadget is accounted for, safely handled, and either reused or repurposed agreeing to industry benchmarks. Proficient IT transfer not as it were mitigates potential dangers but moreover sets up a clear handle for following and overseeing IT gear all through its lifecycle.
With expanding mindfulness around e-waste reusing and the significance of information security, companies are presently prioritizing proficient information annihilation administrations as portion of their IT transfer approach. Legitimate IT Disposal transfer guarantees that delicate data is forever evacuated whereas complying with legitimate and natural directions. Past security, IT transfer procedures too offer assistance organizations recoup esteem from ancient resources, diminish capacity clutter, and contribute to feasible trade hones. By executing comprehensive IT Disposal transfer methods, businesses can secure basic data, maintain their notoriety, and illustrate a commitment to natural duty.
Table of Contents
2. Guide to Understand IT Asset Disposal
IT resource transfer alludes to the organized handle of securely resigning, reusing, or reusing out of date IT hardware, counting computers, servers, capacity gadgets, and organizing equipment. This prepare includes a few vital steps, such as secure information wiping, physical annihilation of capacity media, and naturally capable e-waste reusing. Businesses progressively depend on proficient IT resource transfer administrations to guarantee that their equipment is taken care of safely all through its lifecycle. Appropriate IT transfer makes a difference anticipate delicate information from falling into the off-base hands, diminishes the hazard of administrative punishments, and permits organizations to keep up a clear stock of resigned IT infrastructure.
Understanding IT foundation transfer is basic for companies looking for to diminish operational dangers whereas maximizing the esteem of their ancient resources. By executing certified information pulverization administrations and taking after endorsed e-waste reusing hones, organizations can guarantee that no secret data is uncovered amid the IT transfer prepare. Moreover, capable IT Disposal transfer bolsters natural supportability by redirecting unsafe materials from landfills and recouping important assets for reuse. In general, a well-planned IT transfer procedure shields both commerce information and the environment whereas optimizing resource administration practices.
3. Why Proper IT Data Disposal is Important?
Proper IT transfer is fundamental for shielding touchy trade and client information. Obsolete gadgets such as portable workstations, servers, and capacity drives can gotten to be prime targets for cybercriminals if not taken care of with secure information pulverization administrations. By actualizing proficient IT transfer strategies, organizations guarantee that all private data is totally evacuated, lessening the hazard of information breaches, lawful punishments, and harm to notoriety. This cautious approach not as it were ensures the organization’s operations but moreover reinforces client believe and illustrates a commitment to cybersecurity best practices.
In expansion to information security, IT Disposal transfer plays a basic part in advancing natural maintainability. Electronic squander regularly contains unsafe materials, counting overwhelming metals and harmful chemicals, which can extremely affect biological systems if arranged of despicably. Capable IT Disposal through certified e-waste reusing programs guarantees that these materials are securely recuperated and reused. This prepare minimizes natural hurt, diminishes landfill squander, and contributes to a more economical lifecycle for IT resources, adjusting commerce operations with eco-friendly practices.
4. Why is it Necessary
IT disposal is vital since businesses persistently produce huge volumes of obsolete IT disposal over time, counting desktops, portable workstations, servers, and organizing gadgets. Without legitimate IT resource transfer techniques, organizations hazard collecting unused or ignored equipment that can make security vulnerabilities and operational wasteful aspects. Viably overseeing these resources through organized IT transfer not as it were ensures touchy data but too streamlines stock, diminishes capacity clutter, and moves forward in general asset assignment. By executing a clear IT disposal arrange, companies can guarantee that resigned gear is taken care of capably, whether it is reused, exchanged, or repurposed.
In expansion to operational effectiveness, administrative compliance makes IT disposal transfer unavoidable for most businesses. Numerous divisions require strict adherence to information assurance and natural laws, which makes secure information pulverization administrations an fundamental portion of IT disposalr. Disappointment to comply with these controls can result in overwhelming fines, legitimate complications, and reputational harm. A proficient IT transfer procedure guarantees that companies meet these administrative prerequisites whereas keeping up security and supportability benchmarks, defending both the organization and its stakeholders.
5. How to Prepare Your IT Assets for Disposal
Before starting IT resource transfer, businesses must carefully get ready their hardware to guarantee both security and operational proficiency. Appropriate planning not as it were minimizes the chance of information breaches but too makes a difference organizations maximize the esteem recuperated from resigned IT disposal. By taking a organized approach to IT transfer, companies can oversee portable workstations, desktops, servers, capacity gadgets, and other IT framework capably, keeping up compliance with legitimate and industry measures all through the transfer process.
Key steps in planning IT resources for transfer incorporate conducting a total stock of all IT disposal transfer things, backing up critical information, performing certified information devastation administrations to safely wipe delicate data, expelling company names, resource labels, and distinguishing proof marks, and categorizing resources based on their potential for reuse, resale, or reusing. Taking after these steps guarantees that the IT transfer handle is orderly, secure, and effective, decreasing hazard whereas supporting supportability and maximizing the esteem of resigned IT infrastructure.
- Conduct a total stock of all IT gear transfer items.
- Backup all vital information some time recently starting disposal.
- Perform certified information devastation administrations to wipe touchy data.
- Remove company names, resource labels, and distinguishing proof marks.
- Categorize resources based on reuse, resale, or reusing potential.
6. How to Prepare So That You Get Best Results from Your Asset Disposal
To accomplish the best comes about from IT resource transfer, organizations must center on cautious arranging and selecting the right approach for resigning obsolete IT disposal. A key IT transfer prepare guarantees that resources are overseen safely, delicate information is completely secured, and administrative necessities are met. By prioritizing legitimate arranging, companies can maximize returns on reusable equipment, diminish operational dangers, and streamline the by and large IT disposal transfer workflow.
Key steps to get the most from IT disposal incorporate choosing a certified IT resource transfer supplier, assessing the resale esteem of reusable gear, guaranteeing full compliance with information security directions, planning convenient transfer to anticipate resource deterioration, and archiving the whole IT transfer prepare for straightforwardness. Collaborating with experienced suppliers and taking after these organized steps guarantees that IT gear transfer is secure, productive, and adjusted with both natural and corporate administration goals.
- Choose a certified IT resource transfer provider
- Evaluate resale esteem of reusable equipment
- Ensure compliance with information security regulations
- Schedule opportune transfer to maintain a strategic distance from resource depreciation
- Document the whole IT disposal handle for straightforwardness
7. The Assets You Should Include in Your IT Asset Disposal Plan
An viable IT disposal transfer arrange incorporates a wide run of hardware that organizations utilize on a day by day premise. Recognizing all important resources guarantees that nothing is ignored amid the IT disposal transfer prepare and that all gadgets are overseen safely. By carefully cataloging each piece of equipment, from portable workstations and desktops to servers and capacity gadgets, businesses can arrange a organized IT transfer workflow that mitigates dangers, avoids information breaches, and guarantees compliance with administrative standards.
Key IT resources to incorporate in any IT disposal methodology are tablets, desktops, and tablets; servers and information capacity gadgets; organizing hardware such as switches and switches; portable gadgets and adornments; and fringe gadgets counting printers and scanners. Legitimately dealing with each of these things through secure information annihilation administrations and certified e-waste reusing programs guarantees that delicate data is secured and important components are recouped. By counting all basic gear in the IT disposal arrange, organizations accomplish both operational effectiveness and natural sustainability.
- Laptops, desktops, and tablets.
- Servers and information capacity devices.
- Networking gear such as switches and switches.
- Mobile gadgets and accessories.
- Printers, scanners, and fringe devices.
Essential Assets
Fundamental resources in IT resource transfer are basically gadgets that store, prepare, or transmit delicate trade data. This incorporates difficult drives, solid-state drives, servers, portable workstations, and portable gadgets that may contain private information. These resources require cautious dealing with amid information annihilation administrations to guarantee that all data is totally eradicated, avoiding unauthorized get to and keeping up administrative compliance. Appropriate administration of these basic resources is a foundation of any compelling IT transfer methodology, guaranteeing both security and operational integrity.
Organizations must prioritize secure taking care of and transfer of capacity gadgets such as difficult drives and SSDs, as these regularly contain basic commerce and client information. Certified IT transfer administrations utilize strategies like secure information wiping, degaussing, or physical annihilation to moderate dangers related with information breaches. By centering on these high-value resources, businesses not as it were ensure touchy data but too improve their by and large IT resource transfer forms, guaranteeing compliance, maintainability, and effective asset management.
What Happens Once Your Assets Are at Restore Technology?
Once resources reach a proficient IT disposal transfer supplier like Reestablish Innovation, they enter a organized and profoundly secure prepare planned to secure both information and the environment. Each piece of IT disposal, from portable workstations and desktops to servers and organizing gadgets, is carefully logged, followed, and evaluated to guarantee appropriate taking care of all through the transfer lifecycle. This organized approach to IT transfer guarantees that organizations can unquestionably resign ancient resources without gambling information breaches, administrative infringement, or operational inefficiencies.
The IT disposal prepare at proficient suppliers ordinarily incorporates comprehensive resource examining, certified information pulverization administrations, and ecologically capable e-waste reusing. Each step is fastidiously recorded, giving businesses with full straightforwardness and confirmation of compliance with industry guidelines. By depending on certified IT disposal administrations, companies can accomplish secure information expulsion, recoup esteem from reusable hardware, and contribute to economical commerce hones whereas minimizing dangers related with obsolete IT disposal.
IT Asset Disposition: Secure. Compliant. Sustainable.
IT disposal mien rotates around three fundamental columns: security, compliance, and maintainability. Organizations must plan their IT disposal hones to adjust with these standards, guaranteeing that resigned equipment is taken care of mindfully and effectively. By centering on organized IT transfer, companies can minimize dangers related with information breaches, administrative non-compliance, and inappropriate e-waste taking care of. Actualizing proficient IT transfer methodologies permits businesses to secure delicate data whereas optimizing the administration of obsolete IT assets.
Secure IT disposal shields private information, avoiding unauthorized get to and decreasing potential legitimate liabilities. Compliance guarantees that IT transfer meets industry controls and government benchmarks, dodging fines or reputational harm. In the mean time, supportability accomplished through certified e-waste reusing decreases natural affect and bolsters corporate social obligation activities. By joining security, compliance, and supportability into IT transfer hones, organizations can keep up operational productivity whereas advancing eco-friendly and lawfully compliant solutions.
Benefits
A well-executed IT disposal methodology gives various points of interest for businesses of all sizes, guaranteeing both operational proficiency and information security. By executing legitimate IT transfer hones, organizations can secure delicate commerce and client information through certified information annihilation administrations, such as secure wiping, degaussing, or physical devastation of difficult drives and SSDs. This diminishes the hazard of information breaches, character burglary, and cyberattacks whereas keeping up compliance with security directions. Furthermore, organized IT transfer permits companies to track and record all resigned resources, giving straightforwardness and confirmation of capable taking care of that can fortify client believe and illustrate a commitment to cybersecurity best practices.
Beyond information security, proficient IT disposal essentially upgrades operational proficiency and natural obligation. Dependable IT disposal transfer, counting certified e-waste reusing, guarantees that perilous materials such as lead, mercury, and cadmium are securely evacuated from the environment. It moreover permits businesses to recuperate esteem from reusable IT resources, such as repaired computers, servers, or organizing gadgets, which can be exchanged or redeployed inside. By embracing a organized IT disposal procedure, organizations not as it were minimize squander and diminish their carbon impression but moreover make strides resource administration forms, decrease capacity costs, and contribute to a feasible and secure IT lifecycle that adjusts with both corporate objectives and legitimate prerequisites.
The 3 Top Benefits of a Good IT Asset Disposal Strategy
A solid IT disposal methodology conveys quantifiable results that advantage both the organization and the environment. By executing organized IT disposal, businesses can change obsolete hardware into openings for esteem recuperation, maintainable reusing, and upgraded operational productivity. Appropriate arranging guarantees that each IT resource, from servers and desktops to capacity gadgets, is safely dealt with, decreasing the chance of information breaches and guaranteeing compliance with administrative and natural standards.
Key benefits of a well-executed IT transfer procedure incorporate improved information security through certified information devastation administrations, fetched reserve funds by exchanging or reusing IT gear transfer resources, and made strides brand notoriety through dependable e-waste reusing hones. Secure IT transfer ensures touchy data, whereas reusing and resale programs diminish squander and create extra esteem for the organization. By receiving these techniques, companies not as it were protect their information and comply with legitimate necessities but too illustrate a commitment to maintainability and corporate responsibility.
- Enhanced information security through appropriate information pulverization services.
- Cost investment funds by exchanging or reusing IT disposal assets.
- Improved brand notoriety through mindful e-waste reusing practices.
The 3 Best Practices for IT Asset Disposition
Implementing best hones guarantees that IT resource transfer forms are proficient, secure, and completely compliant with administrative and natural measures. By taking after demonstrated IT transfer hones, organizations can keep up consistency over their IT disposal exercises, minimize operational dangers, and secure delicate commerce and client information. Organized strategies moreover offer assistance streamline the retirement of out of date equipment, making the handle unsurprising, traceable, and adjusted with corporate administration goals.
Key best hones for IT transfer incorporate joining forces with certified IT disposal suppliers, keeping up nitty gritty records of all transfer exercises, and utilizing confirmed information pulverization administrations for total information evacuation. Certified suppliers guarantee that resigned IT disposal is taken care of safely, whereas fastidious record-keeping gives straightforwardness and responsibility. Confirmed information pulverization administrations, counting secure wiping, degaussing, and physical devastation, ensure that touchy data cannot be recouped. By following to these best hones, businesses can accomplish secure, compliant, and feasible IT transfer, defending both information and the environment.
- Partner with certified IT resource transfer providers.
- Maintain nitty gritty records of all transfer activities.
- Use confirmed information pulverization administrations for total information evacuation.
How Much Does IT Disposal Cost?
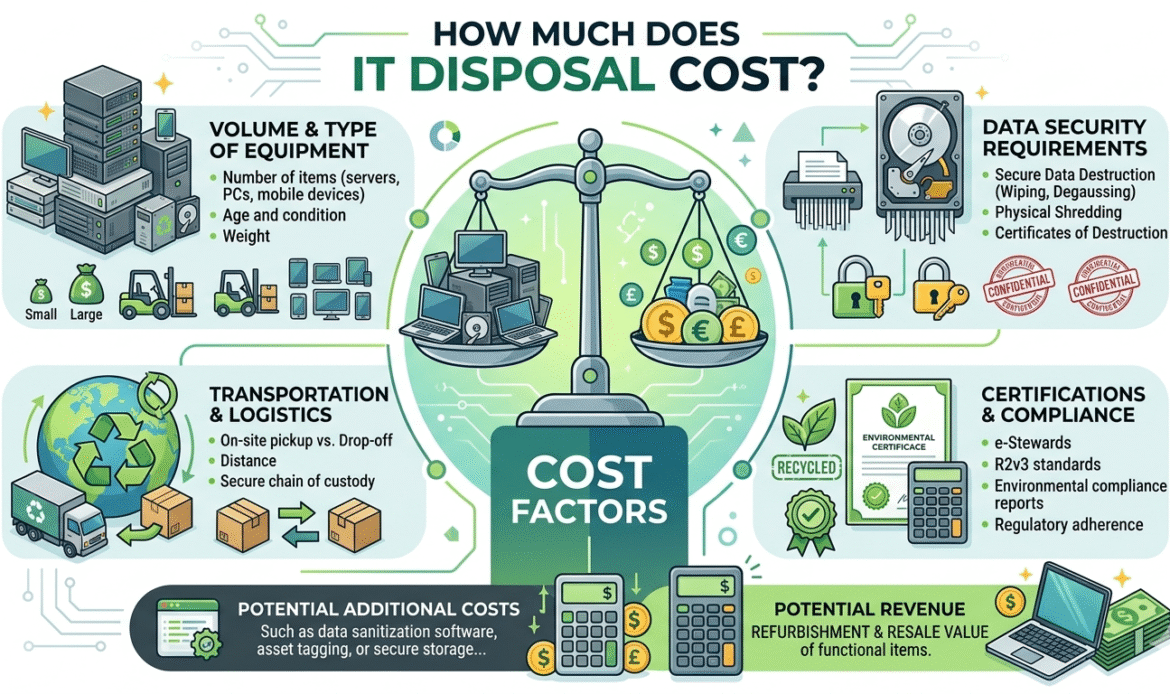
The taken a toll of IT transfer can shift essentially depending on a few variables, counting the sort and amount of gear, the level of information annihilation required, and the coordinations included in transporting resources to certified transfer offices. High-volume organizations with various servers, desktops, portable workstations, and capacity gadgets may confront higher costs due to the scale of secure information wiping and physical devastation administrations required. Also, businesses must consider the complexity of IT framework transfer, counting specialized gear that may require extra dealing with or reusing forms. Appropriate arranging makes a difference companies assess their IT transfer needs and select the most cost-effective arrangement without compromising security or compliance.
While a few IT gear transfer suppliers may offer free pickup for high-value or reusable resources, others may charge for certified information annihilation, transportation, or naturally dependable e-waste reusing. Contributing in proficient IT resource transfer may appear like an forthright cost, but it guarantees long-term investment funds by anticipating exorbitant information breaches, dodging administrative punishments, and minimizing natural risk. By outsourcing IT disposal to trusted suppliers, organizations can defend delicate data, keep up compliance, and accomplish a organized, productive handle for taking care of resigned IT equipment.
Is IT Asset Disposal Necessary for All Companies?
IT disposal is a basic handle for companies of all sizes, whether little businesses, new companies, or expansive endeavors. Any organization that employments advanced gadgets, from portable workstations and servers to organizing hardware and capacity drives, must guarantee that obsolete IT resources are taken care of safely. Without legitimate IT disposal, businesses chance uncovering delicate company and client information, which can lead to expensive breaches, reputational harm, and administrative punishments. Executing a organized IT transfer technique guarantees that resigned gear is overseen mindfully, diminishing operational dangers whereas keeping up compliance with lawful and industry standards.
Even new businesses and littler businesses can harvest critical benefits from proficient IT disposal. Certified information annihilation administrations ensure that all delicate data is forever expelled, whereas capable e-waste reusing guarantees that unsafe materials are securely handled and important components are recouped. By embracing successful IT disposal, organizations of any measure can protect information astuteness, minimize natural affect, and build up a orderly approach to resigning IT foundation. This not as it were ensures the commerce but too illustrates a commitment to maintainability and corporate responsibility.
Future of IT Disposal
The future of IT transfer is quickly advancing as innovative headways and natural mindfulness shape modern industry measures. Organizations are progressively embracing more astute IT resource transfer arrangements that consolidate computerization, real-time following, and economical hones. These developments permit businesses to oversee resigned IT framework more proficiently, guaranteeing that obsolete equipment is safely prepared whereas minimizing the hazard of information breaches. By leveraging progressed IT transfer strategies, companies can streamline operations, diminish costs, and keep up a clear record of all resigned resources all through their lifecycle.
In parallel, developments in certified information pulverization administrations and eco-friendly e-waste reusing are making IT foundation transfer more secure and more dependable. As governments and industry controllers force stricter compliance prerequisites, businesses are prioritizing mindful IT gear transfer hones to stay both lawfully compliant and competitive in the commercial center. Receiving forward-thinking IT transfer techniques not as it were secures delicate data but moreover underpins supportability objectives, decreases natural affect, and positions organizations as mindful, security-conscious pioneers in their industries.
Common Risks of Improper IT Disposal
Improper IT transfer can uncover businesses to genuine dangers that amplify distant past basic information misfortune. When obsolete IT gear such as difficult drives, servers, portable workstations, and capacity gadgets are disposed of without secure IT resource transfer hones, touchy data can frequently be recouped by unauthorized people utilizing essential information recuperation apparatuses. This helplessness can lead to information breaches, personality robbery, monetary extortion, and noteworthy reputational harm. Without certified information devastation administrations as portion of the IT transfer handle, organizations may too come up short to meet lawful and industry compliance prerequisites, expanding the probability of administrative punishments, claims, and long-term money related losses.
In expansion to security concerns, disgraceful IT transfer can have genuine natural results that affect both nearby and worldwide environments. Electronic squander contains unsafe materials such as lead, mercury, and cadmium, which can sully soil and water if not dealt with through certified e-waste reusing programs. Wasteful IT hardware transfer hones may moreover result in missed openings for esteem recuperation, as reusable components and gadgets are disposed of instep of being restored or exchanged. By dismissing organized IT transfer procedures, businesses not as it were contribute to natural corruption but too confront operational wasteful aspects, compliance dangers, and decreased supportability execution over time.
How to Choose the Right IT Disposal Provider
Choosing the right IT transfer supplier is a vital step in guaranteeing that IT disposal is taken care of safely, proficiently, and in full compliance with industry directions. Businesses must carefully assess suppliers based on their certifications, industry encounter, and demonstrated capacity to provide solid information devastation administrations.
A dependable IT transfer accomplice ought to follow to recognized measures such as secure information wiping and physical devastation conventions, whereas keeping up strict chain-of-custody strategies. Straightforwardness is similarly critical, with suppliers advertising point by point announcing, review trails, and certificates of devastation to confirm that all IT resources have been handled mindfully. This level of responsibility makes a difference organizations keep up compliance, decrease chance, and guarantee that touchy information is for all time evacuated without any plausibility of recovery.
Beyond security and compliance, companies ought to moreover evaluate the provider’s commitment to maintainability and capable IT disposal transfer hones. A dependable IT transfer supplier will actualize ecologically mindful e-waste reusing strategies, guaranteeing that dangerous materials are securely dealt with and profitable components are recuperated. Also, suppliers that back restoration and resale of reusable IT resources can offer assistance businesses maximize esteem recuperation and diminish by and large transfer costs.
Components such as secure transportation, real-time resource following, responsive client back, and end-to-end lifecycle administration ought to moreover be considered when selecting a accomplice. By choosing a qualified and forward-thinking IT transfer supplier, businesses can accomplish a secure, compliant, and feasible IT transfer handle whereas moving forward operational proficiency and fortifying their commitment to natural responsibility.
IT Disposal Process Overview
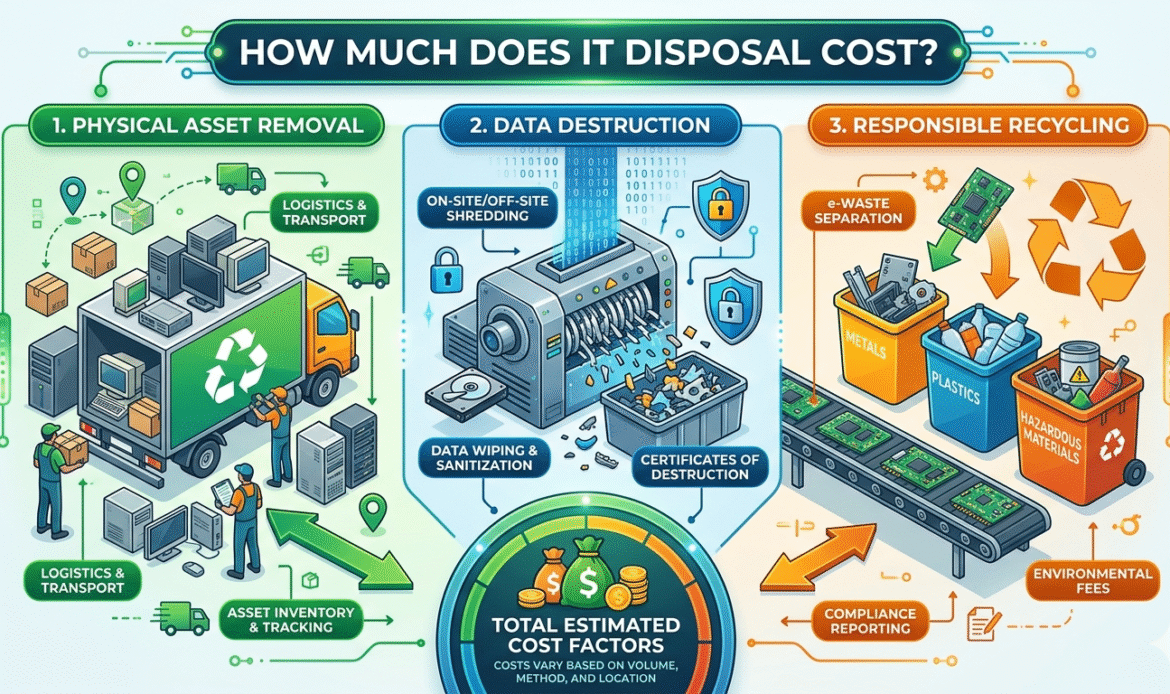
The IT disposal prepare takes after a well-defined and organized lifecycle outlined to guarantee security, administrative compliance, and natural supportability. From the minute IT resources such as portable workstations, servers, and capacity gadgets are resigned, each step is carefully overseen to ensure delicate trade and client information. Certified information devastation administrations are utilized to forever delete data, whereas point by point following and reviewing give straightforwardness and responsibility all through the IT transfer prepare. This organized approach not as it were shields data but too streamlines operations and diminishes the hazard of non-compliance with industry regulations.
Each organize of IT foundation transfer plays a imperative part in maximizing productivity and minimizing natural affect. Appropriate taking care of of resigned IT disposal guarantees that important components are recuperated and reused, whereas perilous materials are securely handled to anticipate natural hurt. By taking after a orderly IT transfer lifecycle, organizations can keep up control over their IT resources, recoup potential esteem from out of date hardware, and actualize feasible hones that adjust with corporate social obligation activities. The combination of security, compliance, and supportability makes proficient IT disposal an fundamental viewpoint of cutting edge commerce operations.
| Step | Process Description |
|---|---|
| Inventory | Identify and document all IT assets |
| Data Destruction | Securely erase or destroy sensitive data |
| Evaluation | Assess resale or recycling potential |
| Recycling | Perform eco-friendly e-waste recycling |
| Certification | Provide proof of secure IT disposal |
Conclusion
IT disposal is no longer only an operational errand; it has gotten to be a basic component of advanced trade methodology. Legitimate IT resource transfer guarantees that delicate trade and client information is secured from potential breaches whereas at the same time supporting natural supportability activities. By coordination IT transfer into their in general operational arranging, organizations can keep up the keenness of their IT framework, diminish administrative dangers, and illustrate a commitment to both security and corporate obligation. Organized IT disposal too makes a difference businesses oversee resigned hardware effectively, guaranteeing that obsolete equipment is either safely reused, exchanged, or repurposed.
Adopting proficient IT disposal and leveraging certified information devastation administrations permits businesses to accomplish results that are secure, compliant, and economical. Mindful IT hardware transfer shields private data, anticipates legitimate and money related liabilities, and bolsters eco-friendly e-waste reusing programs. By contributing in a precise IT disposal procedure nowadays, companies lay the establishment for a more secure, greener, and more productive future, upgrading operational proficiency whereas ensuring both organizational information and the environment.
Learn more about e-waste recycling to protect the environment and secure your personal data.
Frequently Asked Questions
What is IT disposal and why is it important?
IT disposal is the process of securely retiring or recycling outdated IT equipment, including computers, servers, and storage devices. Proper IT asset disposal ensures that sensitive data is destroyed, preventing data breaches, and that equipment is recycled responsibly to reduce environmental impact. By following professional IT disposal practices, businesses protect both their data and reputation.
How do businesses prepare IT assets for disposal?
Preparing IT assets for disposal involves several key steps. First, companies must back up important data and perform certified data destruction services on all storage devices. Next, equipment should be inventoried, labeled, and categorized for reuse, resale, or recycling. Proper preparation ensures that IT disposal is secure, efficient, and compliant with regulations.
What are the benefits of professional IT asset disposal?
Professional IT disposal provides multiple benefits for businesses. It guarantees secure data destruction, ensuring sensitive information does not fall into the wrong hands. It also enables compliance with legal and environmental regulations, supports sustainable e-waste recycling, and can even help recover value from old IT equipment. Overall, IT disposal improves operational efficiency and reduces risk.
How much does IT disposal cost for companies?
The cost of IT disposal varies depending on the type and volume of equipment, data destruction requirements, and recycling services. While some providers may offer free pickup for certain assets, professional IT disposal services often charge for secure data destruction and eco-friendly recycling. Investing in proper IT disposal helps companies avoid costly data breaches and compliance penalties, making it a worthwhile expense.


