Data sanitation goes beyond just some tech jargon in IT. Its basically the way to keep your digital stuff safe from messing up later. Like when you delete a file or swap out an old device or even update a server, there are these leftover bits that stick around. If you dont handle them right, they turn into big problems for security. It seems kind of obvious now, but I didnt think about it that way at first.
Think about it similar to moving out of a place you rent. You wouldnt just leave papers everywhere for the next person to find. Data sanitation is that thorough wipe down, making sure nothing sensitive hangs around when you pass on the hardware or retire it. Businesses deal with so much of this every day. They create heaps of info, customer details, money stuff, passwords, secret reports, all that.
Without doing it properly, that data can pop back up even after you thought it was gone. Then you have breaches, fines from rules, and all sorts of risks for the company. It feels like a lot to manage, but protecting what you have and keeping people trusting you depends on getting this right. Some parts of it get messy to explain, like how exactly the remnants hide. I think implementing good practices is key, though organizations might overlook it sometimes.
Table of Contents
What Is Data Sanitation?
Data sanitation is all about making sure data is permanently wiped from any storage device, like hard drives or USB sticks, so it can’t be recovered. This process also covers servers and backups. In today’s connected world, data constantly accumulates and moves around, so once it’s no longer needed, it must be completely removed to prevent risks.
Organizations handle sensitive information—financial records, customer details, confidential ideas, and private communications. Simple deletion isn’t enough, since deleted files can still linger on devices. Proper data sanitation uses techniques like overwriting, degaussing, or even physical destruction to ensure security and privacy. It also helps businesses stay compliant with regulations, protecting them from potential legal and financial issues.
There are multiple techniques involved, including:
- Overwriting data
- Cryptographic erasure
- Physical destruction
- Degaussing
- Secure data wiping software
Why Data Sanitation Matters More Than Ever
The entire world exists as a data-driven system, which generates dangers whenever data becomes accessible. Each device, which includes hard drives, USBs, and servers, operates silently to store various components of spoken words and financial activities and business plans and personal information. When people throw away outdated or unused technological equipment without cleaning its data, the devices transform into obsolete machines which cybercriminals use as treasure troves. Unused storage locations can develop into secret repositories which contain confidential documents that outsiders can access after they steal the material.
The effects which result from poor data cleaning methods create actual financial damage through identity theft and corporate spying and compliance violations and extensive economic damage. Businesses lose millions of dollars because of data breaches, but the most severe impact occurs when trust erodes, which takes years to establish but only requires moments to destroy. A major security incident can occur because organizations fail to wipe personal devices that they either sold or left unused in storage. The essential organizational task requires organizations to determine whether using the delete function provides proper protection for their confidential data.
The Difference Between Data Deletion and Data Sanitation
| Feature | Data Deletion | Data Sanitation |
|---|---|---|
| Recoverable? | Often yes | No |
| Security Level | Low | High |
| Compliance Ready? | No | Yes |
| Suitable for Disposal? | No | Yes |
| Method | Delete command | Certified wiping/destruction |
Common Methods of Data Sanitation
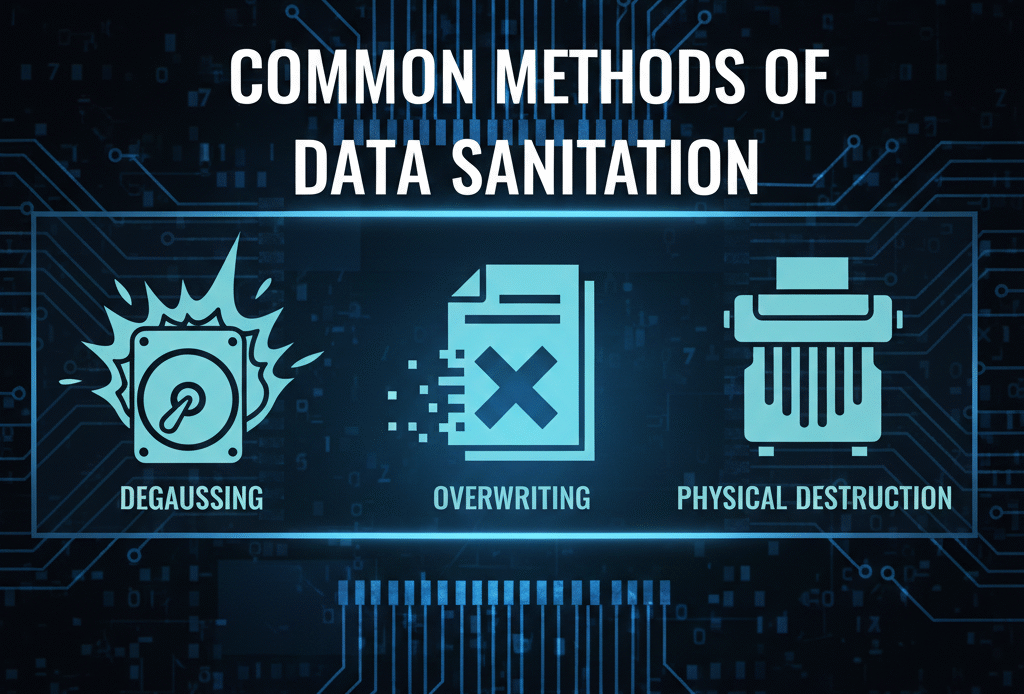
The selection of a data sanitation method requires organizations to acknowledge their need to find a specific solution that meets their unique requirements. The most effective approach depends on the type of storage device, the sensitivity of the information, and applicable regulatory requirements. A corporate server which holds financial records and customer data needs to follow stricter security requirements than a personal USB drive which contains outdated files and schoolwork. The selection of an incorrect method will result in the exposure of important information because it remains open to being retrieved.
Organizations need to manage their data sanitation requirements through both operational scaling and regulatory compliance. Organizations that operate under strict data protection regulations require them to execute complete data deletion procedures which must include both verification and documentation processes. The objective of this process requires us to achieve two goals which need us to delete all material and keep it from being accessed again. The most common data sanitation methods will be examined in this study because they show how organizations protect their confidential information from unauthorized access.
1. Data Overwriting
Data overwriting serves as the fundamental technique for data sanitation because it replaces all existing stored data with either random patterns or designated sequences that overwrite the data multiple times. The process of overwriting goes beyond simple deletion because it removes data from storage by writing new content which completely obscures the original information. The organization implemented this method to ensure that all sensitive data which includes customer records and financial information and proprietary files remains permanently unrecoverable.
Data recovery becomes impossible through recognized industry standards when their execution occurs with industry standards. Organizations find data overwriting to be an economical solution which they can use on traditional hard drives and certain solid-state drives. The system enables organizations to protect their confidential data during equipment reuse and resale processes. The implementation of data overwriting together with a complete data sanitation plan helps businesses secure their confidential information while they continue their daily operations.
2. Degaussing
Degaussing functions as a data cleaning technique which applies strong magnetic fields to disrupt the magnetic fields that store data. The data on a storage device becomes completely unreadable when strong magnetic forces exceed their operational limits. The method guarantees complete and safe destruction of sensitive data which includes financial documents and personal information and confidential corporate materials.
Degaussing works best for magnetic storage devices which include traditional hard drives and magnetic tapes. The method achieves total data destruction results but it makes the device impossible to use after that point. Degaussing becomes the perfect solution for protecting data because it provides maximum security during situations when organizations need to destroy all data. Degaussing serves as a critical element within an effective data disposal program which organizations use to achieve their objectives of permanent data removal.
3. Physical Destruction
The safest and most reliable method for data sanitation requires complete physical destruction of data. The storage devices undergo complete internal component destruction through crushing, shredding, drilling, and incinerating techniques which create complete data recovery obstacles. The physical destruction process guarantees that all sensitive information, which includes customer records and financial data and proprietary intellectual property, will remain protected from unauthorized access. This method functions as the most secure data sanitation solution which organizations need to protect their highly confidential information.
The method gains approval for use with highly sensitive or classified information because it guarantees that no data can be retrieved. The physical destruction process makes it impossible to reuse hardware, yet it delivers a visible and conclusive method to finish the data lifecycle. The organizations which implement physical destruction as part of their data sanitation process can achieve complete elimination of vital data, while they simultaneously protect their systems from unauthorized access and ensure they meet all security and regulatory requirements. Physical destruction functions as the vital element which organizations need to establish powerful data sanitation systems that provide maximum protection.
4. Cryptographic Erasure
Cryptographic erasure uses encryption to protect data which becomes inaccessible without the matching encryption keys. The stored data becomes completely inaccessible when all encryption keys which protect it get deleted or destroyed. The method establishes a security measure which prevents data access and reconstruction from physical storage devices because it protects the data through secure methods of data disposal.
The method operates with high speed and effectiveness which makes it suitable for use in extensive systems that include cloud storage, enterprise servers, and virtualized infrastructure. Organizations use cryptographic erasure to quickly sanitize sensitive information because they do not need to destroy or change the storage device, which lets them keep operational efficiency and compliance. Businesses protect their confidential information through cryptographic erasure, which they use as part of their data sanitation process to decrease the possibility of unauthorized access.
5. Secure Wiping Software
The secure wiping software employs certified tools together with industry-approved methods to perform data destruction from storage devices. The programs execute multiple overwriting passes which extend beyond basic deletion, making it impossible to recover erased data. The secure wiping tools generate comprehensive reports and logs, which establish proof that data sanitation processes have been completed successfully. The organization must keep this documentation because it serves as essential material for compliance audits and regulatory requirements which establish accountability standards while maintaining transparency during data disposal operations.
The corporate and enterprise environments have adopted this method because data security and regulatory compliance together with documentation requirements are vital for their operations. The implementation of secure wiping software allows organizations to delete sensitive data which includes customer records and financial information together with intellectual property. The system provides operational efficiency together with dependable performance and protective measures which establish it as a fundamental element for effective data sanitation procedures. Businesses need secure wiping software because it serves as their essential resource for maintaining continuous data protection while preventing future data breaches.
5 Powerful Benefits of Data Sanitation
Data sanitation functions as both a technical protection method which organizations use to secure their IT systems and as a strategic defense mechanism that protects essential business operations. Every organization stores valuable information and the method of handling data at its end point will determine whether it becomes a security threat or stays as a valuable resource. Through proper sanitation procedures sensitive data will be completely removed from both abandoned devices and obsolete computer systems.
The system provides protection against security threats while establishing enduring business strength. Organizations which implement proper data disposal methods achieve lower risks about security breaches and penalties from regulations and damage to their public image. Responsible data management practices establish trustworthiness which leads to better business relationships with customers. The data sanitation methods which organizations use to protect their information systems provide five significant advantages.
- Protects sensitive customer information
- Prevents identity theft and fraud
- Ensures regulatory compliance
- Maintains brand reputation
- Reduces legal liabilities
Industries That Rely Heavily on Data Sanitation
All industries process information yet different sectors experience distinct hazards. Some organizations require strict compliance with rules because they need to protect highly sensitive data while handling extensive amounts of personal information throughout their daily operations. The industries require data sanitation because it serves as their fundamental security measure which protects their confidential data through permanent and safe destruction methods.
A single mistake during the process of handling confidential documents leads to legal consequences and financial damages and erosion of public confidence. The data sanitation process requires complete accuracy because certain sectors need to follow strict standards for their operational procedures. All organizations from healthcare and finance to government and educational institutions and e-commerce businesses depend on these methods to protect their data while meeting legal requirements.
- Healthcare
- Banking and Finance
- Government Agencies
- Educational Institutions
- E-commerce Companies
5 Costly Mistakes Businesses Make
Data sanitation failures occur in rare cases when people do not understand the process. More often, they result from routine shortcuts, overlooked devices, or seemingly harmless assumptions. The disposal process needs to be executed correctly because any mistake will reveal confidential data which has been kept hidden by the organization for many years.
When organizations treat data removal as an unimportant task instead of following established procedures they create a situation that leads to greater operational risks. What might seem like a minor oversight—an uncleaned backup drive or an unsanitized employee device—can escalate into financial penalties, reputational harm, and operational disruption. The first step to create effective data sanitation systems which safeguard company assets requires understanding these common errors.
- Assuming deletion is permanent
- Ignoring old backup drives
- Not sanitizing employee devices
- Failing to document the process
- Choosing unverified service providers
Data Sanitation for Remote Work Environments
Employees who work remotely depend on their personal laptops and USB drives and cloud storage systems to perform their work tasks. The ability to work from anywhere increases employee productivity but creates additional security challenges which threaten protected corporate information. Any device which departs from the company without proper cleaning procedures becomes a security risk because it can lead to unauthorized access of protected business information which includes customer records and intellectual property and internal communications.
Organizations require secure disposal procedures for all company information which exists on devices used by employees who leave the organization. The implementation of strict offboarding sanitation procedures which include hardware and cloud account and storage media handling procedures will prevent data breaches while meeting security compliance requirements. The organization can use these protocols to transform all its potential security weaknesses into secure operational procedures which will protect both its confidential information and its organizational reputation.
Cloud Data Sanitation Explained
Organizations believe that data transfers to the cloud will remove all requirements for data cleaning because they think this process works. The business must handle sensitive data protection because cloud providers establish both security measures and deletion procedures. When organizations depend entirely on their service providers, they create security gaps that put their confidential information at risk of being accessed by unauthorized users.
Verification serves as the fundamental requirement needed to achieve successful cloud data sanitation procedures. Businesses need to assess all aspects of their provider’s data retention policies and backup storage methods and server decommissioning protocols and encryption key management systems and compliance certification processes. Cloud storage systems without this proper investigation process become dangerous because they share the same security vulnerabilities as traditional on-premises systems. The organization needs to implement data sanitation procedures for the cloud environment because this process will help them achieve three objectives which include protecting confidential information and maintaining legal requirements and preserving their organizational reputation.
- Data retention policies
- Backup storage practices
- Server decommissioning procedures
- Encryption key management
- Compliance certifications
5 Essential Steps in a Data Sanitation Policy
The process of establishing a successful data sanitation policy begins when organizations locate their sensitive data assets. Organizations need to identify which files and databases and devices hold their vital information which includes customer records and financial data and intellectual property and confidential communications. Businesses protect their assets effectively when they assign proper security measures according to their understanding of each asset value and sensitivity and their essential information disposal process.
A selection of the appropriate sanitation methods needs to proceed with documentation of procedures and ongoing staff training. Employees must understand both the techniques used and the reasons behind them to ensure proper execution. Organizations use periodic audits to check compliance with regulations while discovering process shortcomings which they can use to advance their organizational improvement efforts. A properly implemented data sanitation policy establishes a secure process which protects sensitive information throughout all organizational functions.
Common Misconceptions About Data Sanitation
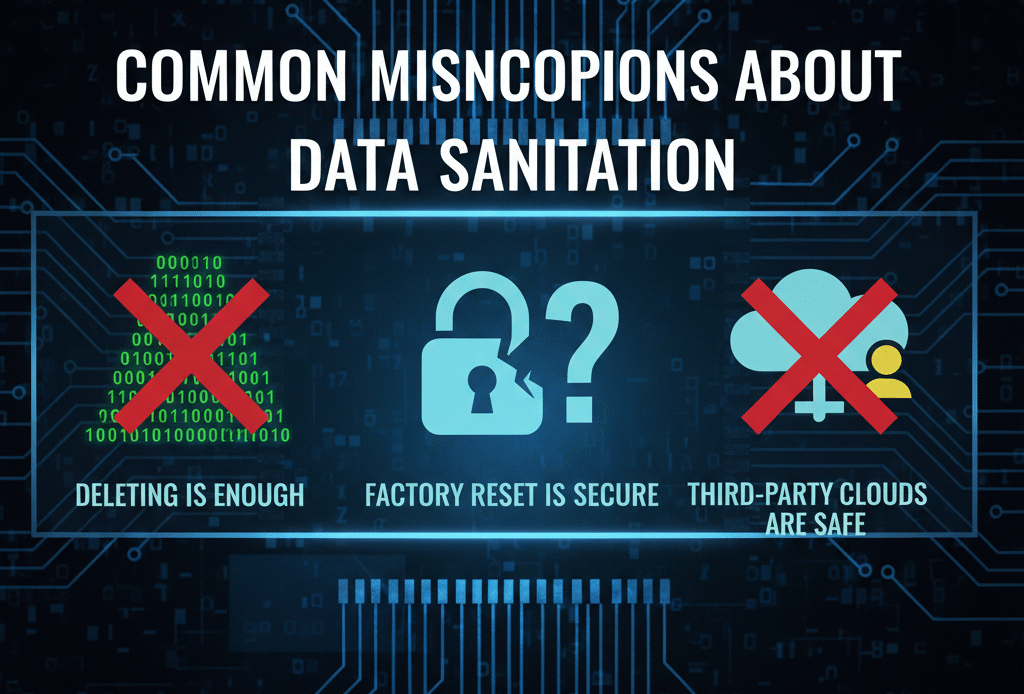
Various organizations fail to comprehend the full meaning of data sanitation which results in their making dangerous assumptions and developing insufficient security methods. People believe that pressing “delete” or formatting a device will completely erase all information from the system which is a common fallacy. The process of deleting files from a system does not make them permanently inaccessible because specialized software can restore deleted files which creates a risk of exposing sensitive information when proper sanitation methods are not used.
Another common misconception holds that only large businesses and organizations which operate in highly regulated sectors need to perform data sanitation work. All business sizes manage important information which leads to data breaches and identity theft incidents as well as regulatory fines through even minor mistakes. Some people believe that using cloud storage and encryption methods provides complete data protection but organizations must take responsibility for ensuring their information gets deleted from all storage systems. Organizations need to comprehend these false beliefs to establish data sanitation methods that work correctly and produce trustworthy results.
Tools and Software for Effective Data Sanitation
Your training includes data up until the month of October in the year 2023. The correct software tools serve as the essential foundation for effective data sanitation which enables organizations to permanently delete their sensitive information. Organizations can securely erase data from multiple storage devices through certified wiping programs and degaussing machines and encryption management solutions. The security and compliance requirements of the industry standards receive full protection through these tools, which create authentic security, and compliance reports that follow industry requirements.
The secure data wiping software system automatically handles the process of data overwriting through its information deletion functions, while degaussing devices work to disable magnetic storage systems. Cryptographic erasure tools destroy encryption keys for encrypted data, which makes the information inaccessible without needing to change the physical device. Through these tools organizations can establish an organized data sanitation system that operates efficiently while creating a trackable process to decrease security breaches and achieve complete storage platform compliance with regulations.
Data Sanitation for Mobile Devices
Mobile devices—which include smartphones and tablets and smartwatches—keep large volumes of private information which consists of emails and contacts and banking data and confidential business documents. The process of data deletion becomes more difficult because mobile devices provide dual data synchronization through various cloud storage systems and application platforms which require users to use special procedures for complete data removal. The process of deleting applications and executing a factory reset will not achieve complete removal of all existing data.
Organizations need to follow three steps for mobile device security which involve using dedicated mobile data deletion software and implementing complete device encryption before data disposal and deleting all cloud backups associated with the device. Organizations need to destroy devices through physical methods when they need to protect confidential information which requires highest security standards. The implementation of thorough mobile device cleaning procedures enables organizations to safeguard their sensitive data while stopping unauthorized access and meeting their legal requirements for data security.
Emerging Trends in Data Destruction Technology
Data destruction methods are undergoing development to match the increasing data volumes and advancements in storage technology. Organizations can now use automated systems to conduct extensive data cleaning operations without requiring human operators. Businesses can now use real-time monitoring and compliance tracking systems to confirm their data has been permanently deleted while they follow regulatory standards.
The adoption of new storage technologies requires organizations to acquire new destruction techniques which apply specifically to cloud-native systems and solid-state drives and hybrid architectures. Organizations are turning to cryptographic erasure and advanced degaussing techniques and AI-powered sanitation solutions because these methods deliver faster and more efficient and dependable results. Organizations must implement advanced solutions to achieve secure data destruction because data destruction has become a customized process which requires tailored methods in today’s fast-changing digital environment.
Cost-Benefit Analysis of Data Sanitation
The data pollution control process requires ongoing financial investment yet produces benefits that continue to accumulate over time. Organizations achieve effective data sanitation through two main outcomes which include protecting private data and their defense against expensive security breaches together with their defense against law enforcement fines which protect their corporate image. When compared to the potential financial and reputational damage caused by a single security lapse, the investment in proper sanitation tools, software, and training is minimal.
The use of structured data sanitation methods enables organizations to operate their operations more effectively. The automatic sanitation procedure secures equipment for safe reuse while generating cost savings through reduced need for physical assets. The analysis of costs against risks shows that businesses should invest in complete data sanitation processes because this method brings about multiple advantages which include maintaining compliance and enhancing security and building customer trust.
Environmental Impact of Data Sanitation
The most effective way to protect data through physical destruction of storage devices leads to environmental problems because destroyed equipment becomes electronic waste which needs proper disposal methods. Organizations need to manage their electronic waste because hardware destruction through crushing, shredding, and incineration does not provide total security. Organizations today need to find ways to protect sensitive data while they work to establish environmentally sustainable operations.
The certified recycling providers work together with partners to ensure safe and environmentally friendly processing of destroyed devices. The providers establish two security measures because they prevent data retrieval and they handle component recycling in an environmentally responsible manner which decreases the ecological impact of waste electronics. Organizations achieve security and sustainability results through data sanitation methods which use proper recycling procedures to protect sensitive data while reducing environmental damage.
The Future of Data Sanitation
The ongoing growth of AI and IoT together with the increasing production of data creates a situation which requires more sophisticated data cleaning methods. Modern storage technologies which include cloud-native architectures and next-generation memory devices require new data sanitation methods to achieve permanent and secure disposal of confidential data. The current digital environment requires organizations to adopt better data protection methods because even minor mistakes can result in major data leaks.
Conclusion: Clean Data, Clear Future
Data sanitation stands as an essential duty because it serves as a protective measure which maintains trustworthiness throughout our modern digital environment. The organization treats every data element which includes customer information and internal messages as highly important because leaving it unprotected resembles leaving money unattended in a public space. Proper data sanitation procedures delete all confidential data which creates a safer environment because it stops breaches and identity theft and unauthorized access. All businesses must implement strict data sanitation practices because they face significant risks to their operations.
Explore another insightful article to deepen your understanding for E Waste Recycling
Frequently Asked Questions
What is data sanitation?
Data sanitation is the process of permanently removing or destroying data from storage devices so it cannot be recovered. It goes beyond simple deletion, ensuring sensitive information is fully protected.
Why is data sanitation important for businesses?
Data sanitation prevents breaches, identity theft, and legal penalties. It protects customer data, maintains trust, and ensures compliance with regulations like GDPR.
What are common methods of data sanitation?
Common methods include overwriting data, degaussing, physical destruction, cryptographic erasure, and using certified wiping software to ensure permanent removal.
Can data sanitation be applied to cloud storage and mobile devices?
Yes! Cloud providers follow structured deletion policies, and mobile devices require secure wiping of internal storage, SIM cards, and SD cards to prevent data leaks.


